mirror of
https://github.com/goauthentik/authentik
synced 2026-04-25 17:15:26 +02:00
b5a92b783f839b4fa9548aece650831ca801a039
* providers/oauth2: require client_secret on device_code exchange for confidential clients
TokenParams.__post_init__ only ran the client_secret check for the
authorization_code and refresh_token grant types:
if self.grant_type in [GRANT_TYPE_AUTHORIZATION_CODE, GRANT_TYPE_REFRESH_TOKEN]:
if self.provider.client_type == ClientTypes.CONFIDENTIAL and not compare_digest(
self.provider.client_secret, self.client_secret,
):
raise TokenError("invalid_client")
The device_code path (__post_init_device_code) then looked up the
DeviceToken solely by device_code and issued an access token if one
matched. A caller that knows the client_id and has stolen a
device_code (e.g. via the standard phishing flow: attacker starts
device authorization, sends user_code to a victim, victim completes
authorization, attacker redeems the device_code) did not have to
prove ownership of the confidential client.
RFC 6749 Section 2.3.1 requires confidential clients to authenticate
to the token endpoint, and RFC 8628 Section 3.4 inherits that: the
device_code is bearer-shaped but not a substitute for client
credentials. Keycloak and Okta both enforce client_secret on the
device token exchange for confidential clients; we didn't.
Add GRANT_TYPE_DEVICE_CODE to the list so the existing compare_digest
check runs for it too. Public clients are unaffected (the guard is
gated on ClientTypes.CONFIDENTIAL). client_credentials/password keep
their own client-auth path in __post_init_client_credentials, which
also enforces the secret (and supports client assertion).
Fixes #20828
Signed-off-by: SAY-5 <SAY-5@users.noreply.github.com>
* Apply suggestion from @BeryJu
Signed-off-by: Jens L. <jens@beryju.org>
* update tests
Signed-off-by: Jens Langhammer <jens@goauthentik.io>
---------
Signed-off-by: SAY-5 <SAY-5@users.noreply.github.com>
Signed-off-by: Jens L. <jens@beryju.org>
Signed-off-by: Jens Langhammer <jens@goauthentik.io>
Co-authored-by: SAY-5 <SAY-5@users.noreply.github.com>
Co-authored-by: Jens L. <jens@beryju.org>
Co-authored-by: Jens Langhammer <jens@goauthentik.io>
ci: bump calibreapp/image-actions from 4f7260f5dbd809ec86d03721c1ad71b8a841d3e0 to e2cc8db5d49c849e00844dfebf01438318e96fa2 (#21812)
web: bump @sentry/browser from 10.48.0 to 10.49.0 in /web in the sentry group across 1 directory (#21810)
core: bump github.com/Azure/go-ntlmssp from 0.1.0 to 0.1.1 in the go_modules group across 1 directory (#21807)
core: bump github.com/Azure/go-ntlmssp from 0.1.0 to 0.1.1 in the go_modules group across 1 directory (#21807)
What is authentik?
authentik is an open-source Identity Provider (IdP) for modern SSO. It supports SAML, OAuth2/OIDC, LDAP, RADIUS, and more, designed for self-hosting from small labs to large production clusters.
Our enterprise offering is available for organizations to securely replace existing IdPs such as Okta, Auth0, Entra ID, and Ping Identity for robust, large-scale identity management.
Installation
- Docker Compose: recommended for small/test setups. See the documentation.
- Kubernetes (Helm Chart): recommended for larger setups. See the documentation and the Helm chart repository.
- AWS CloudFormation: deploy on AWS using our official templates. See the documentation.
- DigitalOcean Marketplace: one-click deployment via the official Marketplace app. See the app listing.
Screenshots
| Light | Dark |
|---|---|
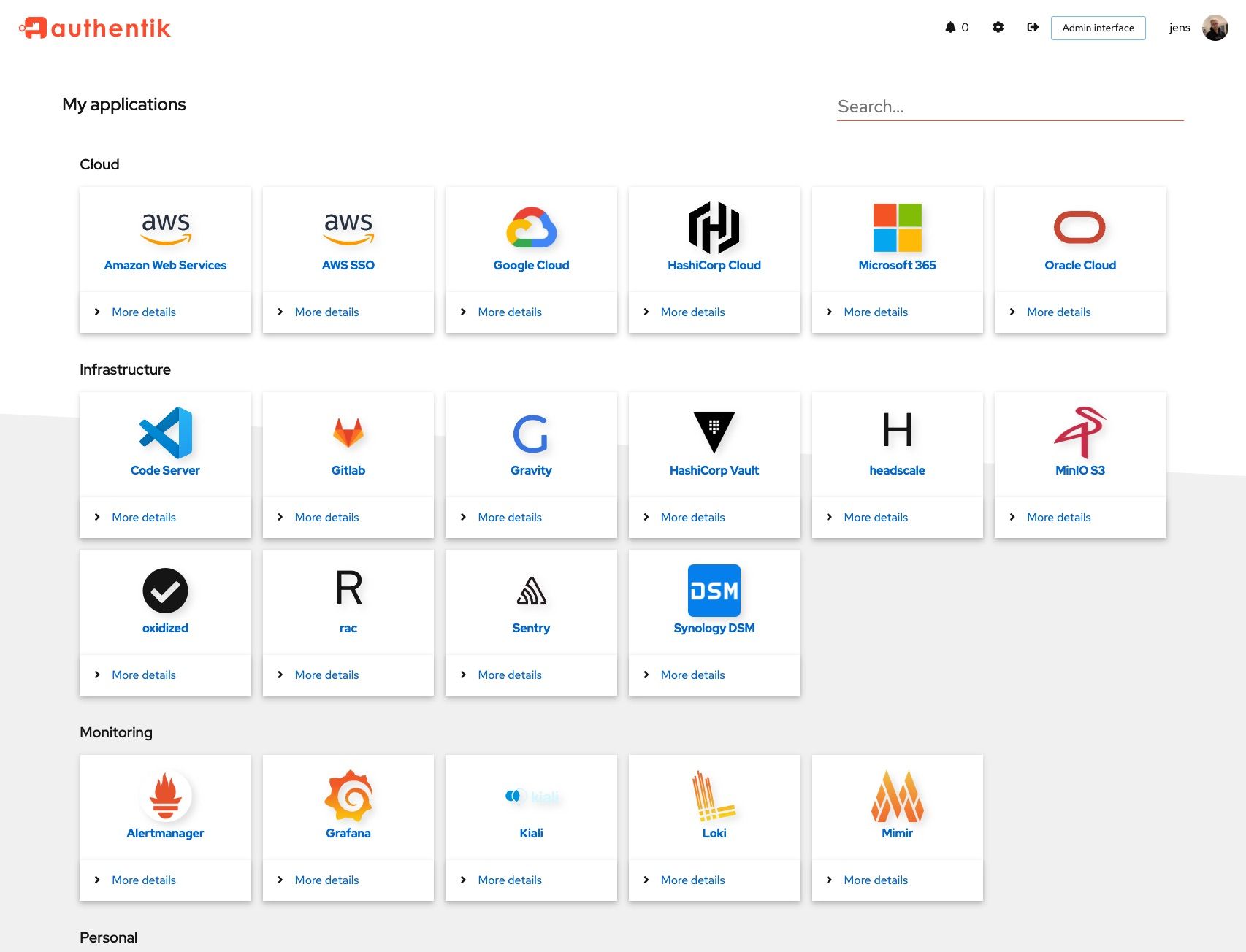 |
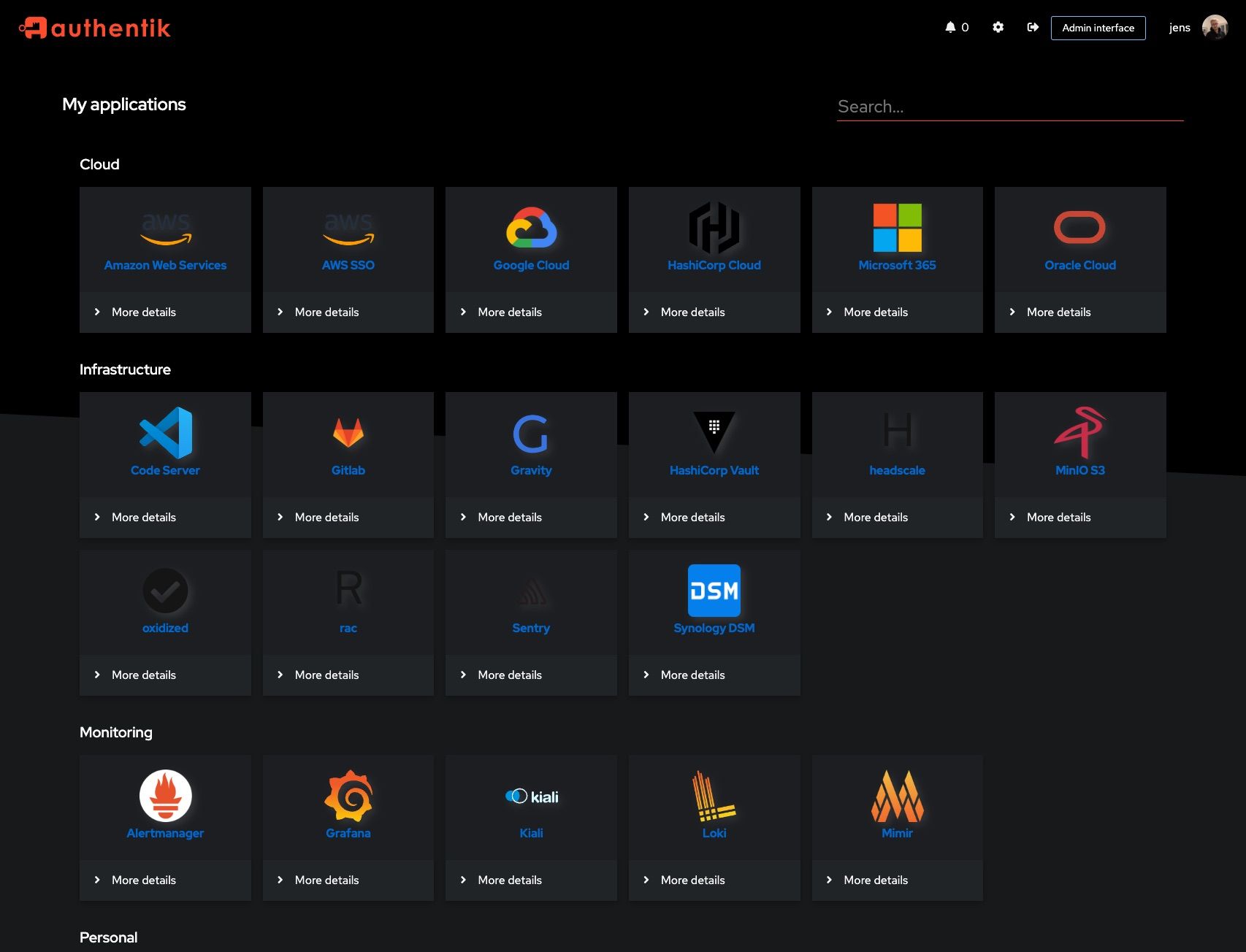 |
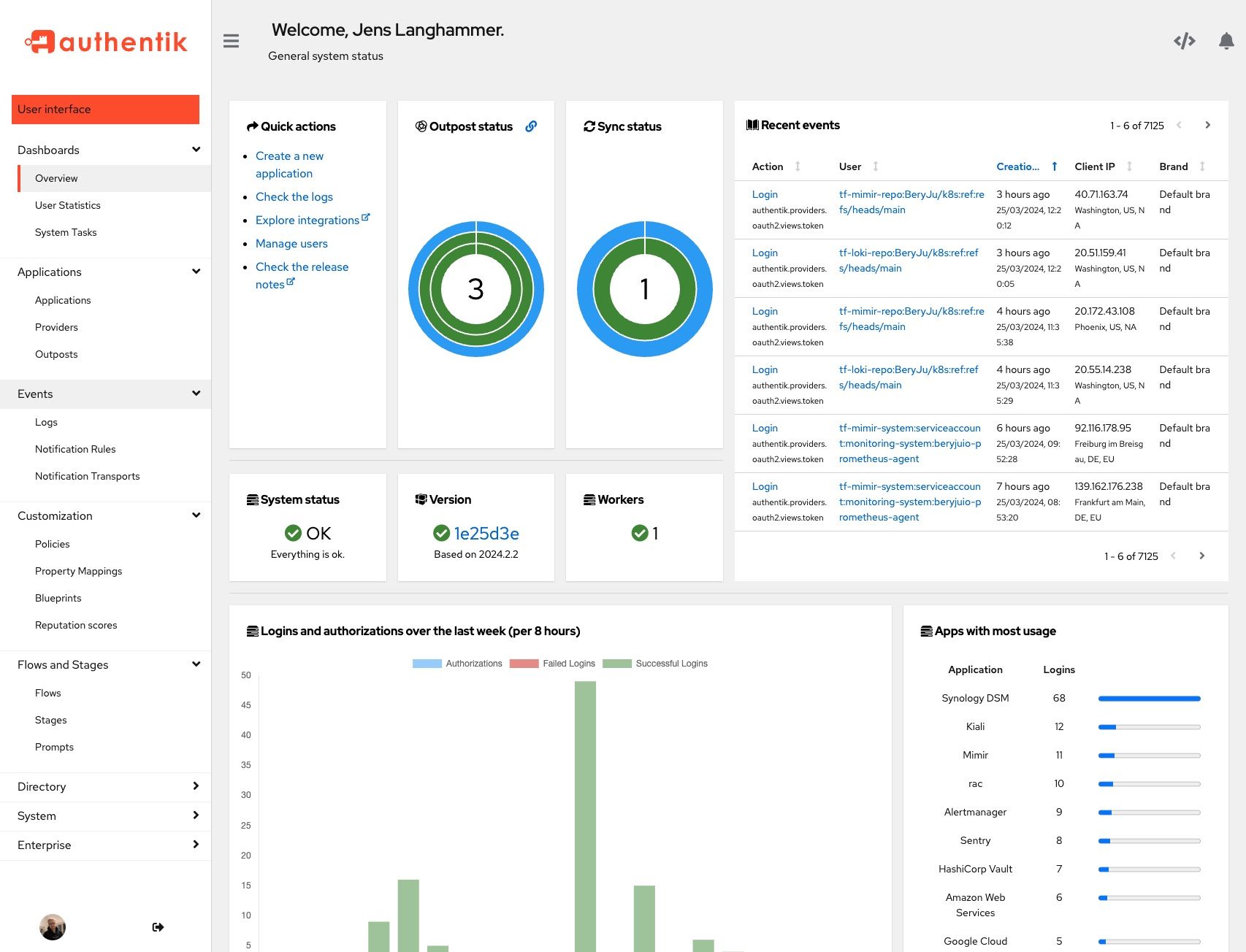 |
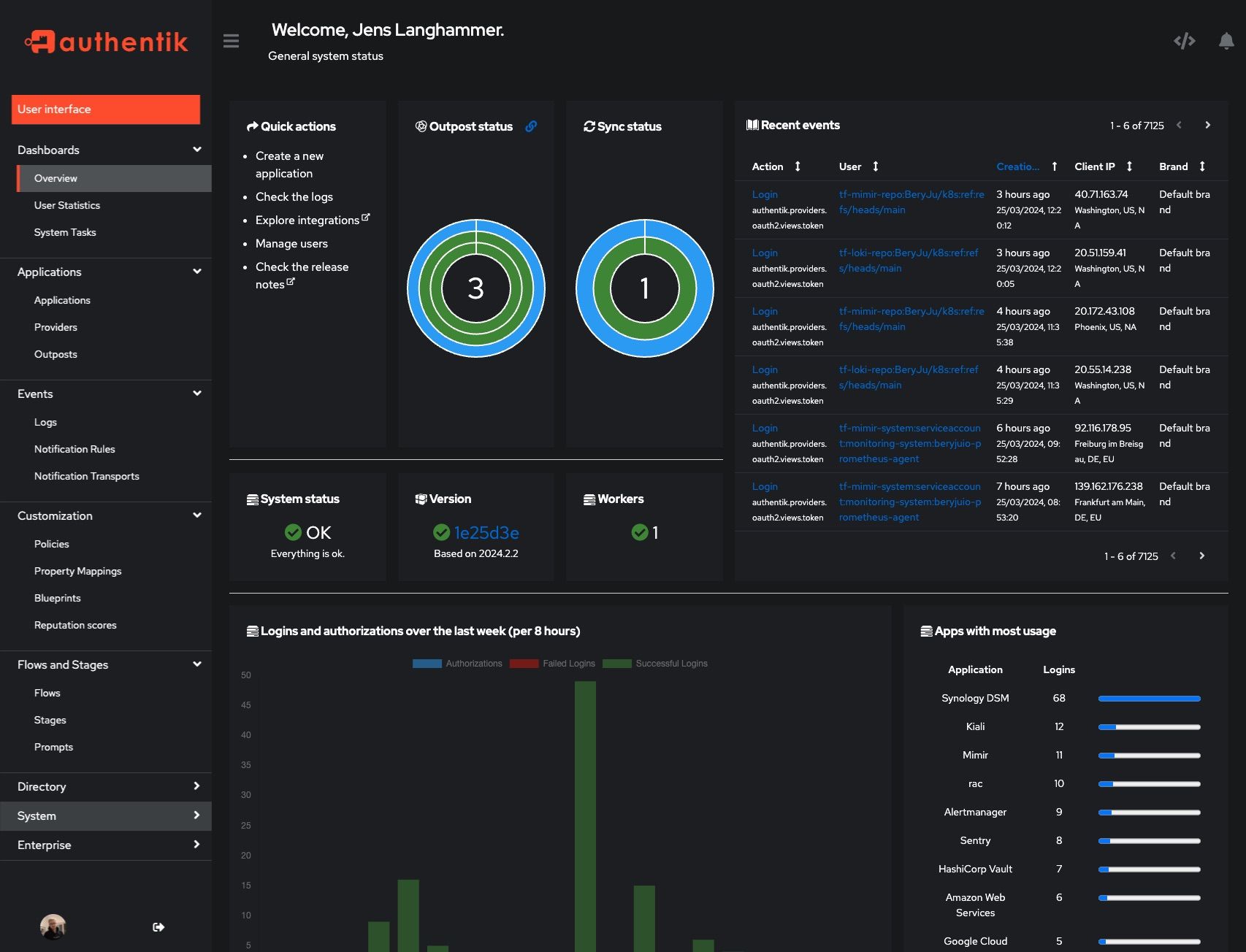 |
Development and contributions
See the Developer Documentation for information about setting up local build environments, testing your contributions, and our contribution process.
Security
Please see SECURITY.md.
Adoption
Using authentik? We'd love to hear your story and feature your logo. Email us at hello@goauthentik.io or open a GitHub Issue/PR!
License
Languages
Python
54.9%
TypeScript
34.9%
Go
4.4%
CSS
2.1%
JavaScript
1.5%
Other
2.1%









