mirror of
https://github.com/goauthentik/authentik
synced 2026-04-25 17:15:26 +02:00
c6b5869b488b07ddd598d1f8066d3d054ae806c0
* stages/user_write: refuse to write id/pk claims onto the user model When an enrollment or source flow maps IdP-supplied attributes onto the User model, update_user walks each key and, if the user already has an attribute by that name, calls setattr(user, key, value) unconditionally. "id" is always present on the User model (it is the Django PK), so a SAML assertion that ships an "id" claim, e.g. a hex string from mocksaml, was written straight into the PK field. Django then rejected the save: ValueError: Field 'id' expected a number but got '<hex>'. The log surfaced as "Failed to save user" and the enrollment flow silently failed for every incoming user. Treat "id" and "pk" the same way the existing "groups" entry is treated: add them to disallowed_user_attributes so the walker logs and skips them. IdP attributes can still be stored on user.attributes via the dotted/underscored forms (e.g. attributes.id), which go through write_attribute and land in the JSONField safely. Added a regression test covering both id and pk in the prompt context. Fixes #21580 Signed-off-by: SAY-5 <SAY-5@users.noreply.github.com> * fix lint Signed-off-by: Jens Langhammer <jens@goauthentik.io> --------- Signed-off-by: SAY-5 <SAY-5@users.noreply.github.com> Signed-off-by: Jens Langhammer <jens@goauthentik.io> Co-authored-by: SAY-5 <SAY-5@users.noreply.github.com> Co-authored-by: Jens Langhammer <jens@goauthentik.io>
What is authentik?
authentik is an open-source Identity Provider (IdP) for modern SSO. It supports SAML, OAuth2/OIDC, LDAP, RADIUS, and more, designed for self-hosting from small labs to large production clusters.
Our enterprise offering is available for organizations to securely replace existing IdPs such as Okta, Auth0, Entra ID, and Ping Identity for robust, large-scale identity management.
Installation
- Docker Compose: recommended for small/test setups. See the documentation.
- Kubernetes (Helm Chart): recommended for larger setups. See the documentation and the Helm chart repository.
- AWS CloudFormation: deploy on AWS using our official templates. See the documentation.
- DigitalOcean Marketplace: one-click deployment via the official Marketplace app. See the app listing.
Screenshots
| Light | Dark |
|---|---|
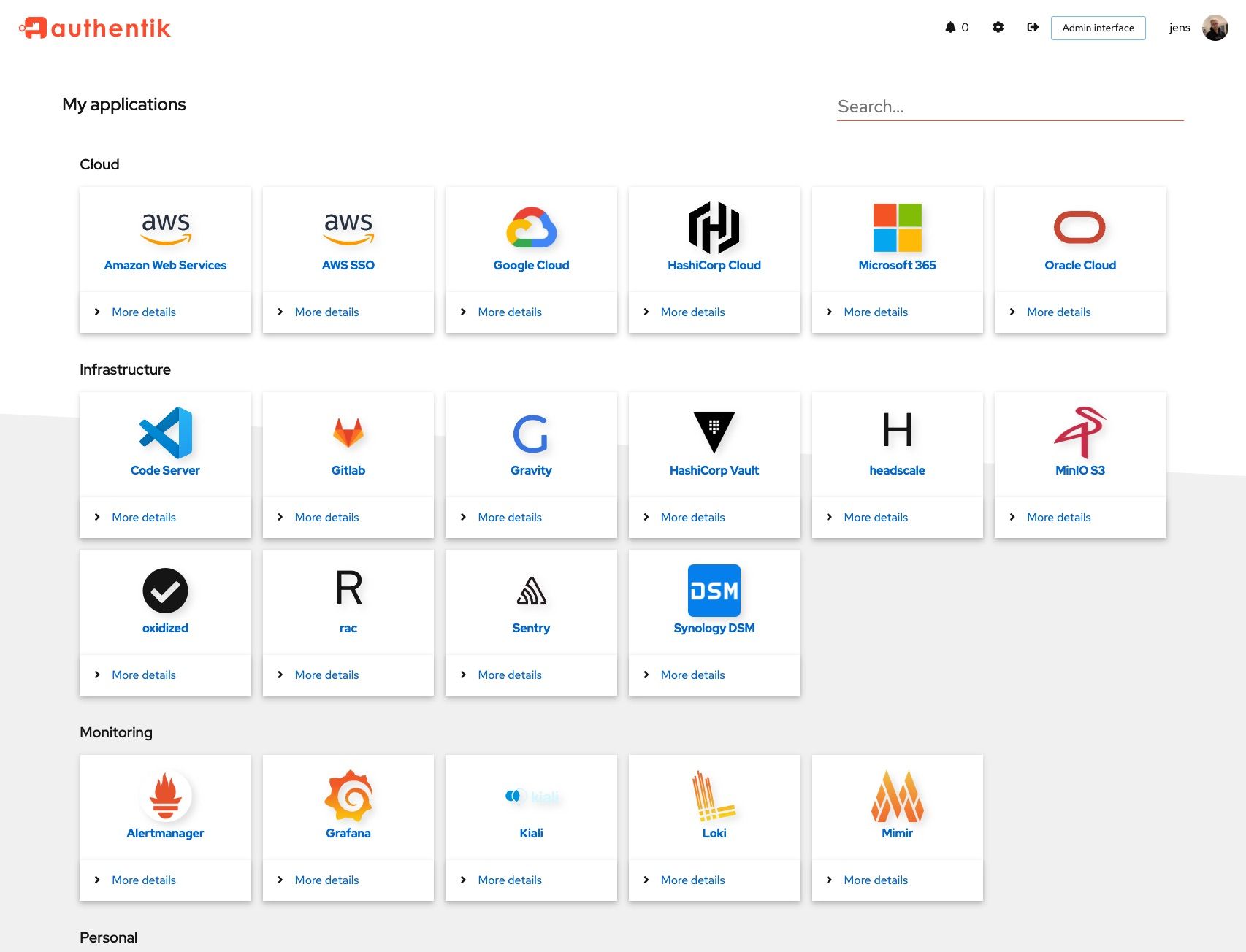 |
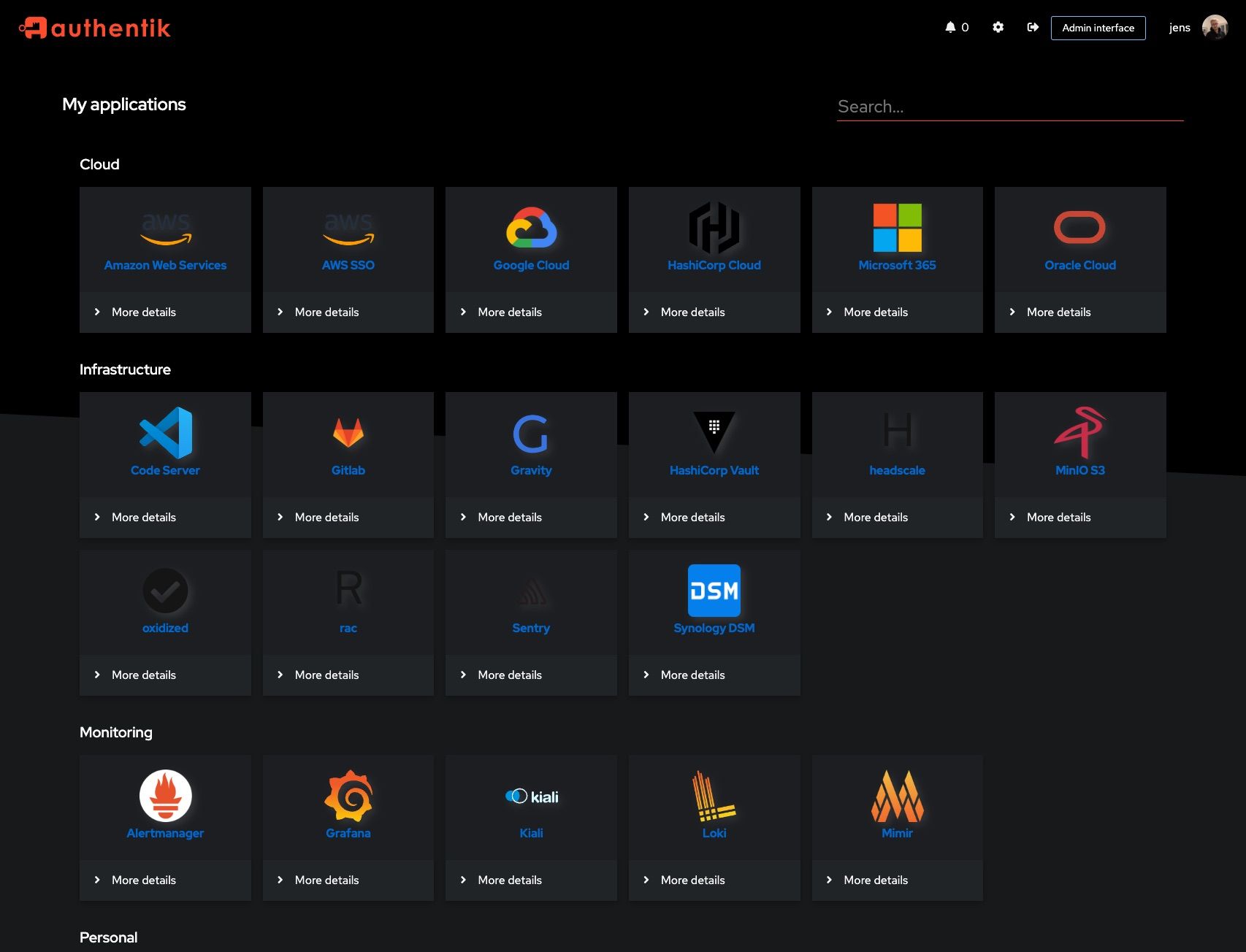 |
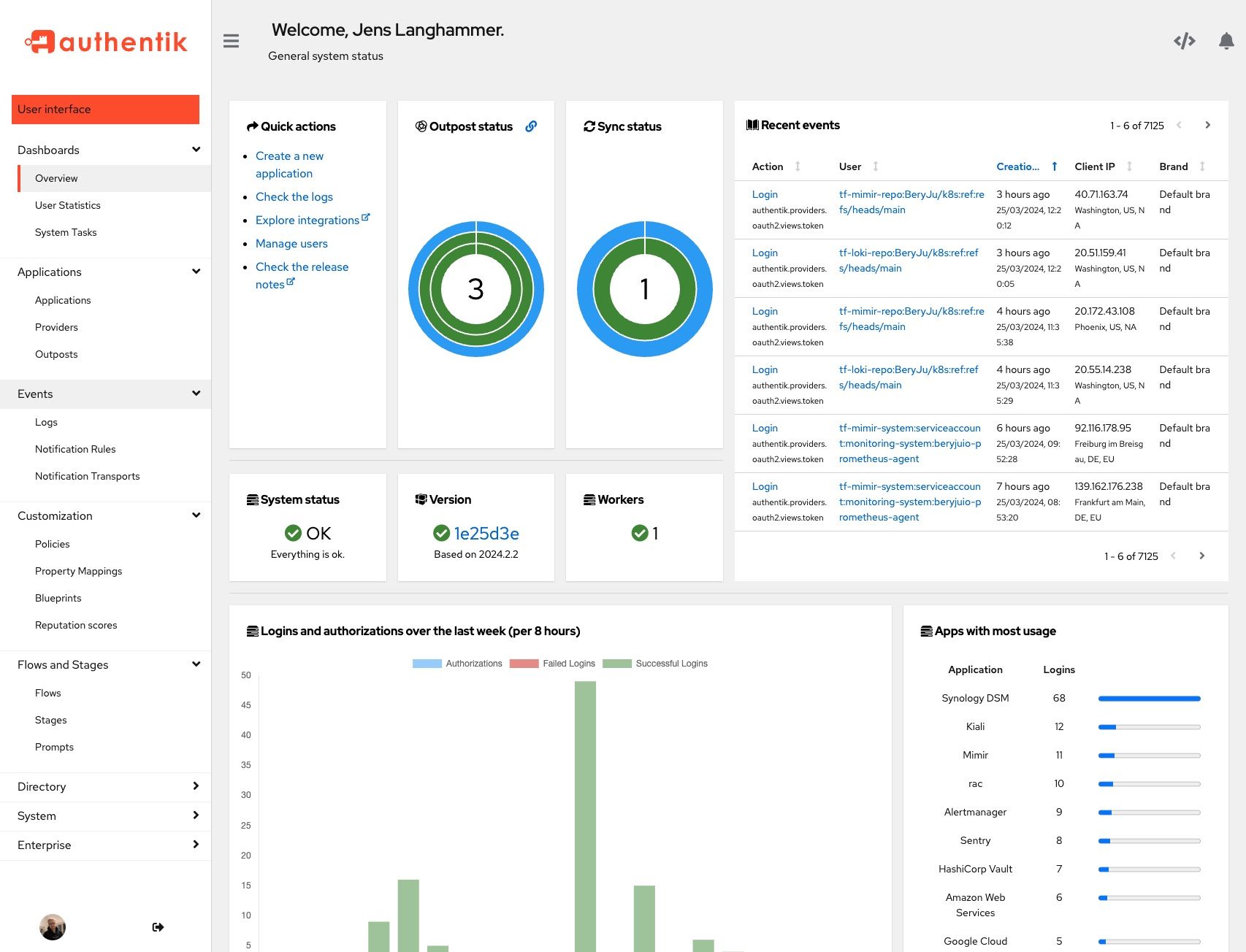 |
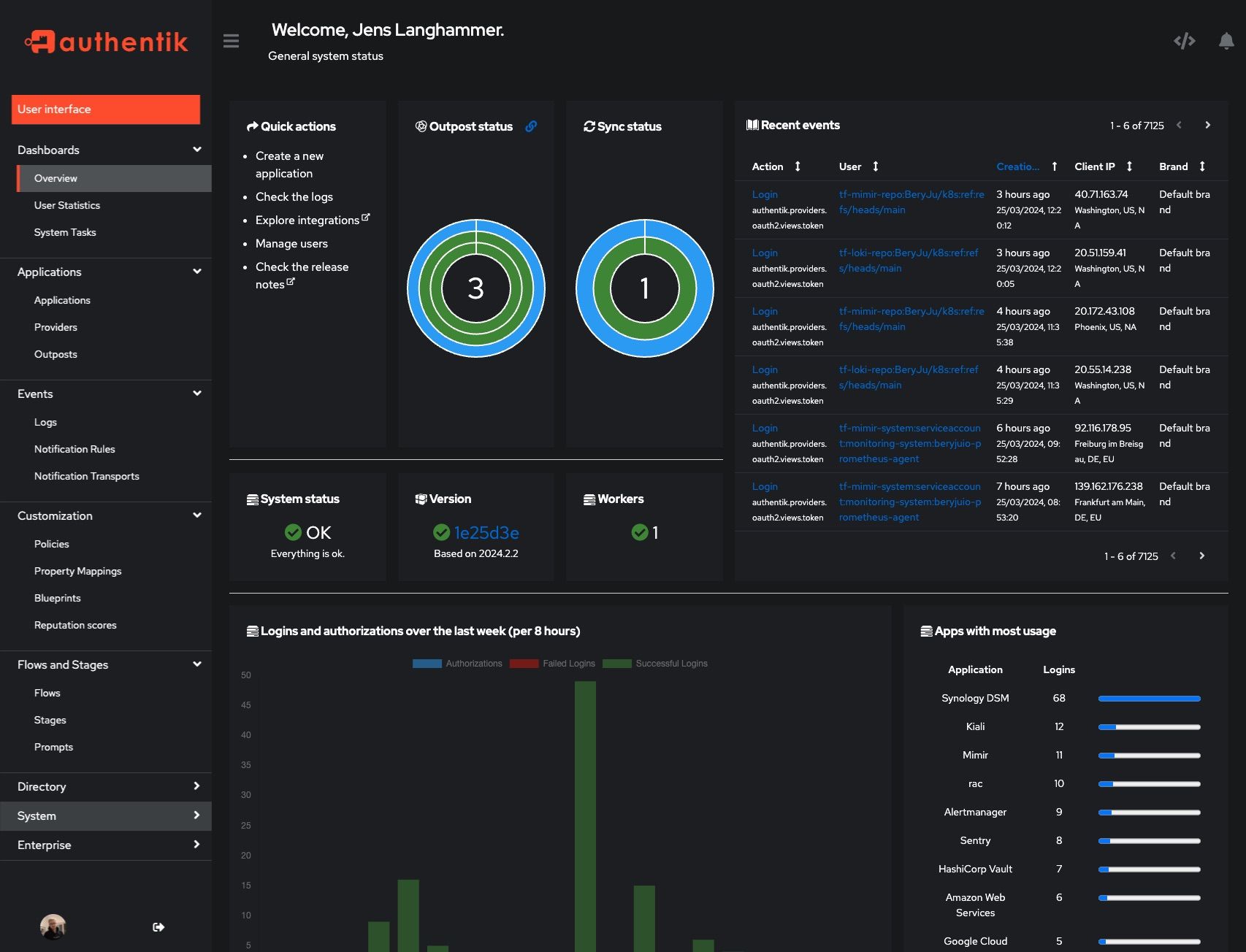 |
Development and contributions
See the Developer Documentation for information about setting up local build environments, testing your contributions, and our contribution process.
Security
Please see SECURITY.md.
Adoption
Using authentik? We'd love to hear your story and feature your logo. Email us at hello@goauthentik.io or open a GitHub Issue/PR!
License
Languages
Python
54.9%
TypeScript
34.9%
Go
4.4%
CSS
2.1%
JavaScript
1.5%
Other
2.1%









