mirror of
https://github.com/goauthentik/authentik
synced 2026-04-25 17:15:26 +02:00
cce646b132229d531b1a868099794615e42fda66
* providers/oauth2: clip device authorization scope against the provider's ScopeMapping set
DeviceView.parse_request stored the raw request scope straight onto the
DeviceToken:
self.scopes = self.request.POST.get("scope", "").split(" ")
...
token = DeviceToken.objects.create(..., _scope=" ".join(self.scopes))
The token-exchange side then reads those scopes back directly:
if SCOPE_OFFLINE_ACCESS in self.params.device_code.scope:
refresh_token = RefreshToken(...)
...
so a caller that adds offline_access to the device authorization
request body gets a refresh_token at the exchange, even when the
provider has no offline_access ScopeMapping configured. Every other
grant type clips scope against ScopeMapping for the provider inside
TokenParams.__check_scopes, but the device authorization endpoint
runs before TokenParams is ever constructed, so the clip never
happens for the device flow.
Combined with #20828 (missing client_secret verification on device
code exchange for confidential clients, now being fixed separately)
and the lack of per-app opt-out for the device flow, this gives any
caller that knows the client_id a path to an offline refresh token
against any OIDC application the deployment exposes.
Intersect the requested scope set with the provider's ScopeMapping
names before we ever persist the DeviceToken. offline_access that is
not configured is silently dropped, matching __check_scopes on the
other grant types. Configured offline_access still flows through
unchanged.
Fixes #20825
Signed-off-by: SAY-5 <SAY-5@users.noreply.github.com>
* rework and add tests
Signed-off-by: Jens Langhammer <jens@goauthentik.io>
---------
Signed-off-by: SAY-5 <SAY-5@users.noreply.github.com>
Signed-off-by: Jens Langhammer <jens@goauthentik.io>
Co-authored-by: SAY-5 <SAY-5@users.noreply.github.com>
Co-authored-by: Jens Langhammer <jens@goauthentik.io>
What is authentik?
authentik is an open-source Identity Provider (IdP) for modern SSO. It supports SAML, OAuth2/OIDC, LDAP, RADIUS, and more, designed for self-hosting from small labs to large production clusters.
Our enterprise offering is available for organizations to securely replace existing IdPs such as Okta, Auth0, Entra ID, and Ping Identity for robust, large-scale identity management.
Installation
- Docker Compose: recommended for small/test setups. See the documentation.
- Kubernetes (Helm Chart): recommended for larger setups. See the documentation and the Helm chart repository.
- AWS CloudFormation: deploy on AWS using our official templates. See the documentation.
- DigitalOcean Marketplace: one-click deployment via the official Marketplace app. See the app listing.
Screenshots
| Light | Dark |
|---|---|
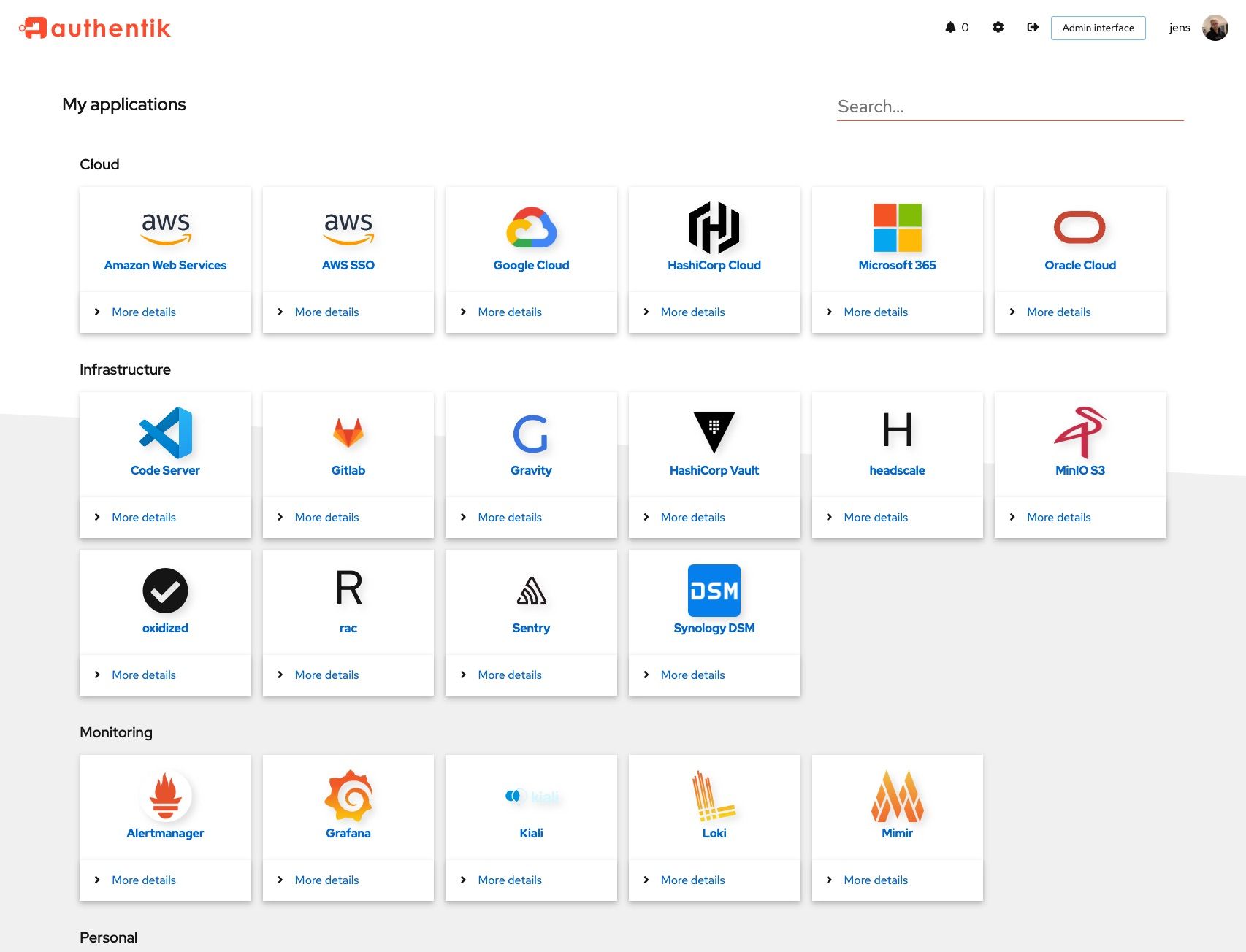 |
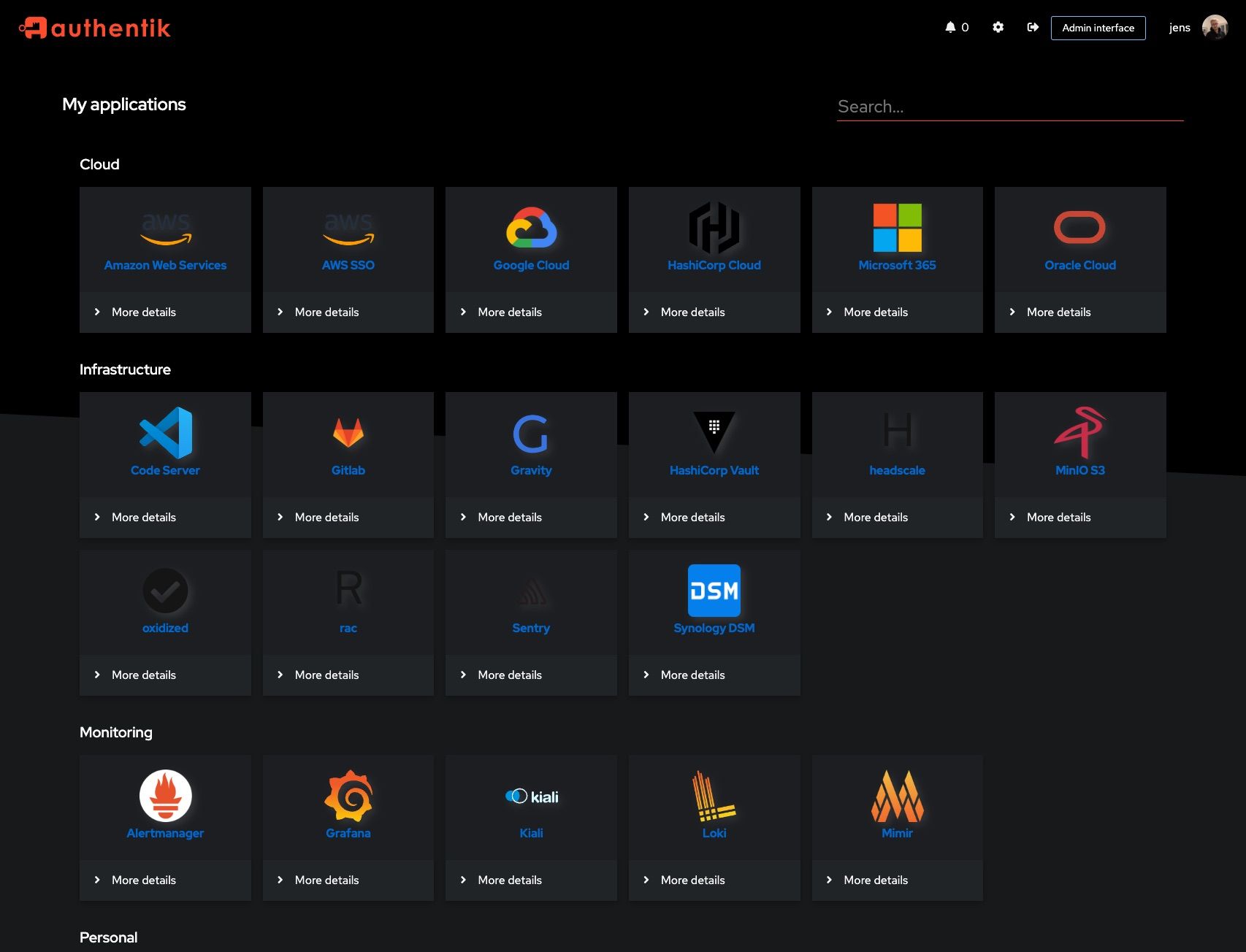 |
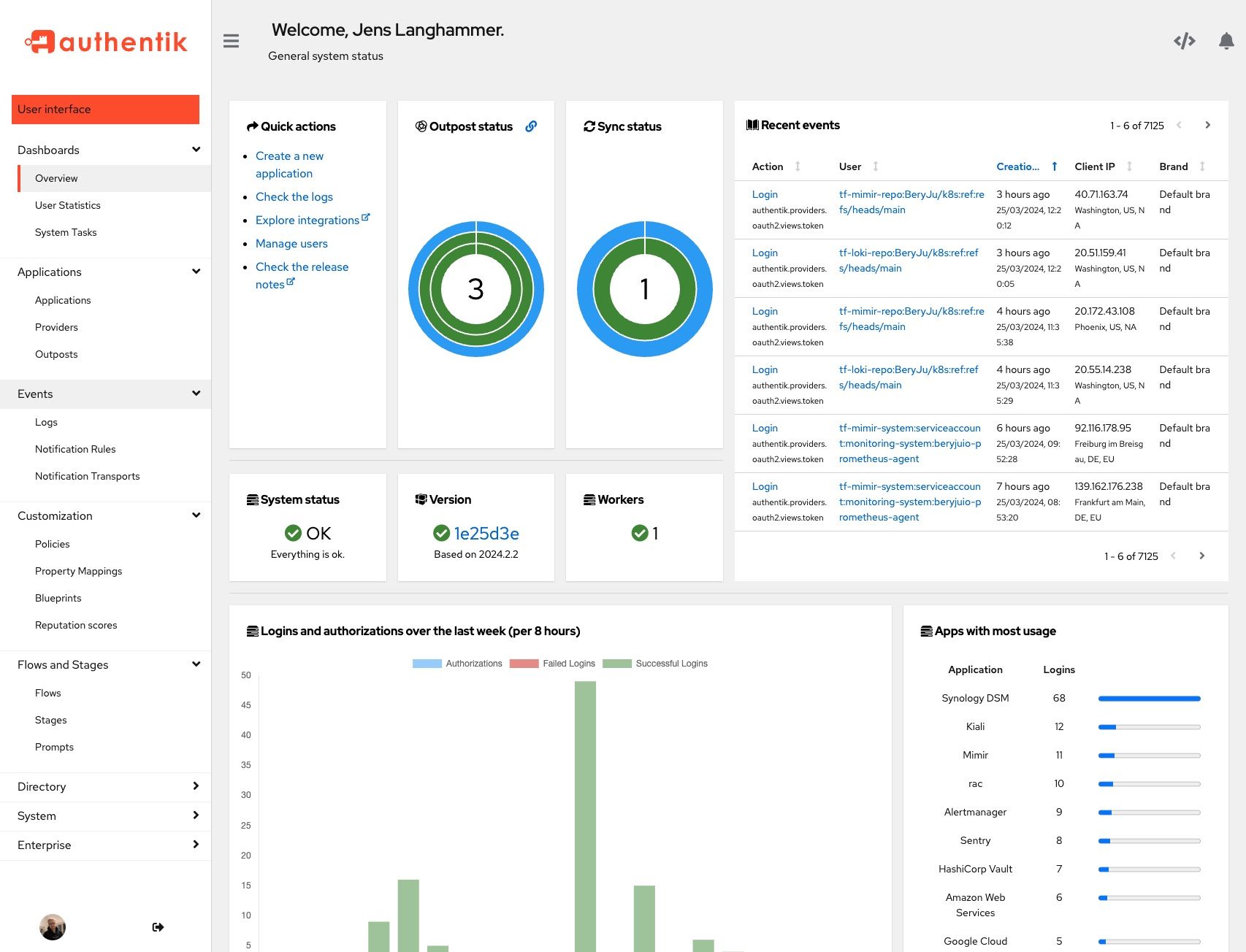 |
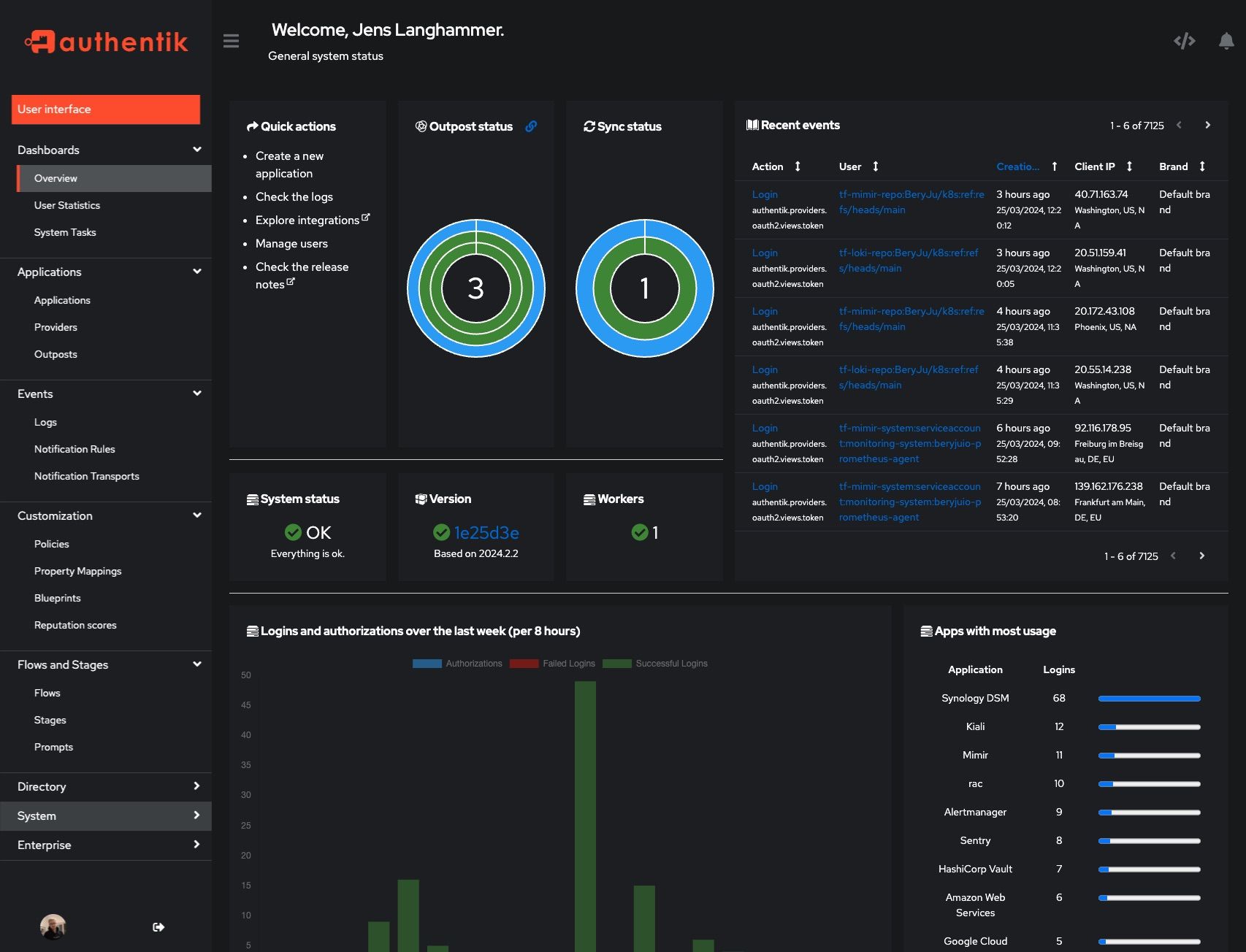 |
Development and contributions
See the Developer Documentation for information about setting up local build environments, testing your contributions, and our contribution process.
Security
Please see SECURITY.md.
Adoption
Using authentik? We'd love to hear your story and feature your logo. Email us at hello@goauthentik.io or open a GitHub Issue/PR!
License
Languages
Python
54.9%
TypeScript
34.9%
Go
4.4%
CSS
2.1%
JavaScript
1.5%
Other
2.1%









