mirror of
https://github.com/goauthentik/authentik
synced 2026-05-10 17:12:08 +02:00
e4ef898feccbc0cb4613401ac744e33a193b2197
Boots the full authentik stack (postgres + Go server + Rust worker) inside the existing ci-web workflow, applies migrations and the test-admin user blueprint, then runs `corepack npm run --prefix web test:e2e` against http://localhost:9000. Uploads the HTML report, traces/videos, and authentik logs as artifacts on failure so reviewers can debug without rerunning locally. Also enables the HTML reporter and screenshot/video capture on CI in playwright.config.js, and updates the full dev-environment docs to point at the same npm scripts CI uses so local and CI runs stay in lockstep. Closes #21994 Co-Authored-By: Agent (authentik-i21994-better-mobile-tangelo) <279763771+playpen-agent@users.noreply.github.com> ci/web: make test-admin blueprint self-contained The previous blueprint used !Find to look up the authentik Admins group, which raced against system/bootstrap.yaml and resolved to None when the explicit apply_blueprint step ran before the worker had applied bootstrap. The serializer rejected groups: [None] with Invalid pk "None". Define the group in the same blueprint with state: present and reference it via !KeyOf, so the test admin setup does not depend on any pre-existing data. If bootstrap has already created the group, state: present is a no-op on the identifiers; otherwise the group is created here. Co-Authored-By: Agent (authentik-i21994-better-mobile-tangelo) <279763771+playpen-agent@users.noreply.github.com> ci/web: format test-admin-user.yaml with prettier Pick up the 4-space indent that web/'s prettier config enforces. The file was added under issue #21994 with 2-space indent and tripped the ci-web format check on push. Co-Authored-By: Agent (authentik-i21994-better-mobile-tangelo) <279763771+playpen-agent@users.noreply.github.com> Use parallelism. Remove guard. Reorder tests. Ignore playwright-traces. Update expected path. Always parallel. Flesh out types. ci/web: post Playwright result comment + gated S3 upload + !cancelled() guards Three reviewer-facing improvements to the e2e job: 1. Idempotent PR comment summarising Playwright pass/fail/flaky/skipped counts. Marker `<!-- playwright-result -->` lets re-runs edit the same comment instead of piling up. Skipped on fork PRs where the default GITHUB_TOKEN is read-only. 2. Optional S3 publish of the HTML report to `s3://authentik-playwright-artifacts/pr-<n>/run-<id>/attempt-<n>/`, gated behind `vars.PLAYWRIGHT_S3_ENABLED == 'true'`. The bucket is pending infra provisioning; the public URL pattern is already wired into the comment so flipping the variable on later requires no workflow changes. Borrows the OIDC + IAM role plumbing from `.github/workflows/release-publish.yml`. 3. Switch the failure-guarded reporting/upload steps to `!cancelled()` so a superseded (cancelled) run no longer emits failure-shaped noise, and so successful runs still produce the artifact bundle reviewers expect. Adds the Playwright JSON reporter so the parse step can pull pass/fail counts from `playwright-report/results.json` for the comment body. Co-Authored-By: Agent (authentik-i21996-internal-achievable-raisin) <279763771+playpen-agent@users.noreply.github.com> web/e2e: fix three regressions blocking the parallel suite Locally and in CI the new `e2e (playwright)` job appeared to "hang" under `fullyParallel: true` + `workers: "50%"`. The hang was actually five tests sharing two unrelated bugs that all manifest as 30s test timeouts; the cluster only *looks* like a parallelism issue because multiple workers stall on the same wall-clock window. With these three fixes the full suite is green in 1m48s on `--workers=2` (was: 5 failed / 17 passed in 5m30s). 1. `web/test/browser/600-providers.test.ts` PR #21647 dropped the `to:` argument on the `session.login()` call in this file's `beforeEach`. Without it, `SessionFixture.login()` waits for the auth-flow URL pattern to re-appear — which it does immediately, since we just navigated there — so the helper returns *before* the post-login redirect lands. The wizard buttons probed afterward live on `/if/admin/#/core/providers`, which the user never actually reaches; every test in the file then hits the 30s `beforeEach` timeout. Pin the destination explicitly, matching the shape of every other test file. 2. `web/src/admin/roles/ak-role-list.ts` The role-list row anchor had no aria-label, so its accessible name was the (random, generated) role name. `500-roles.test.ts` searches for that anchor with `getByRole("link", { name: "view details" })` — the same selector `400-groups.test.ts` uses against the group list, where `GroupListPage.row()` *does* set `aria-label="View details of group ..."`. Bring the role row to parity with groups; the test wasn't wrong, the UI was missing the accessibility hook. 3. `web/test/browser/500-roles.test.ts` ("Edit role from view page") The post-edit verification used `page.getByText(updatedName)`, but on the role view page the new name renders in two places (the "Role <name>" page-navbar heading and the description-list value), so the bare text match resolves to two elements and trips strict-mode. Add `{ exact: true }` so we assert the canonical value the edit wrote rather than the heading template. Co-Authored-By: Agent (authentik-i21996-internal-achievable-raisin) <279763771+playpen-agent@users.noreply.github.com> Use headless.
What is authentik?
authentik is an open-source Identity Provider (IdP) for modern SSO. It supports SAML, OAuth2/OIDC, LDAP, RADIUS, and more, designed for self-hosting from small labs to large production clusters.
Our enterprise offering is available for organizations to securely replace existing IdPs such as Okta, Auth0, Entra ID, and Ping Identity for robust, large-scale identity management.
Installation
- Docker Compose: recommended for small/test setups. See the documentation.
- Kubernetes (Helm Chart): recommended for larger setups. See the documentation and the Helm chart repository.
- AWS CloudFormation: deploy on AWS using our official templates. See the documentation.
- DigitalOcean Marketplace: one-click deployment via the official Marketplace app. See the app listing.
Screenshots
| Light | Dark |
|---|---|
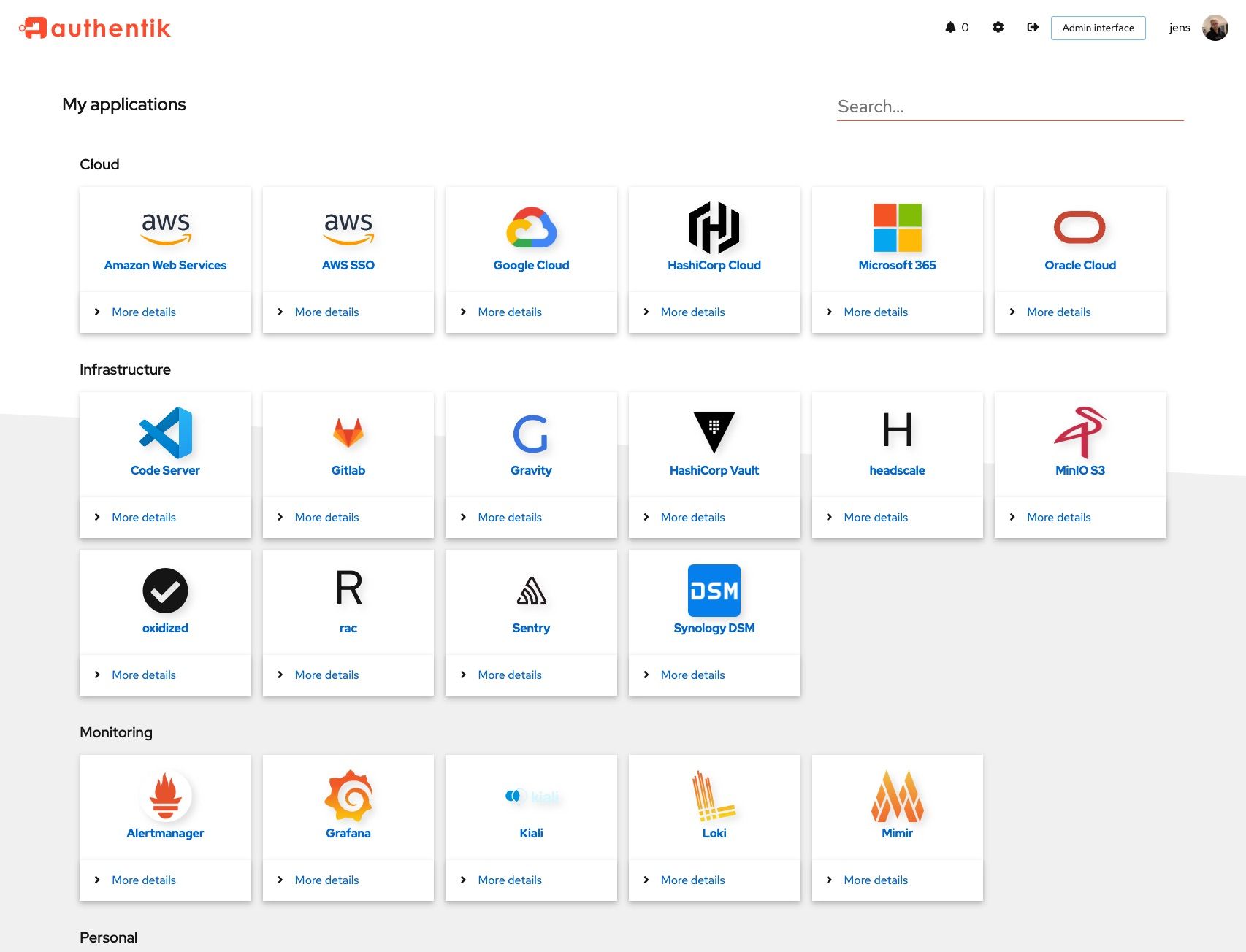 |
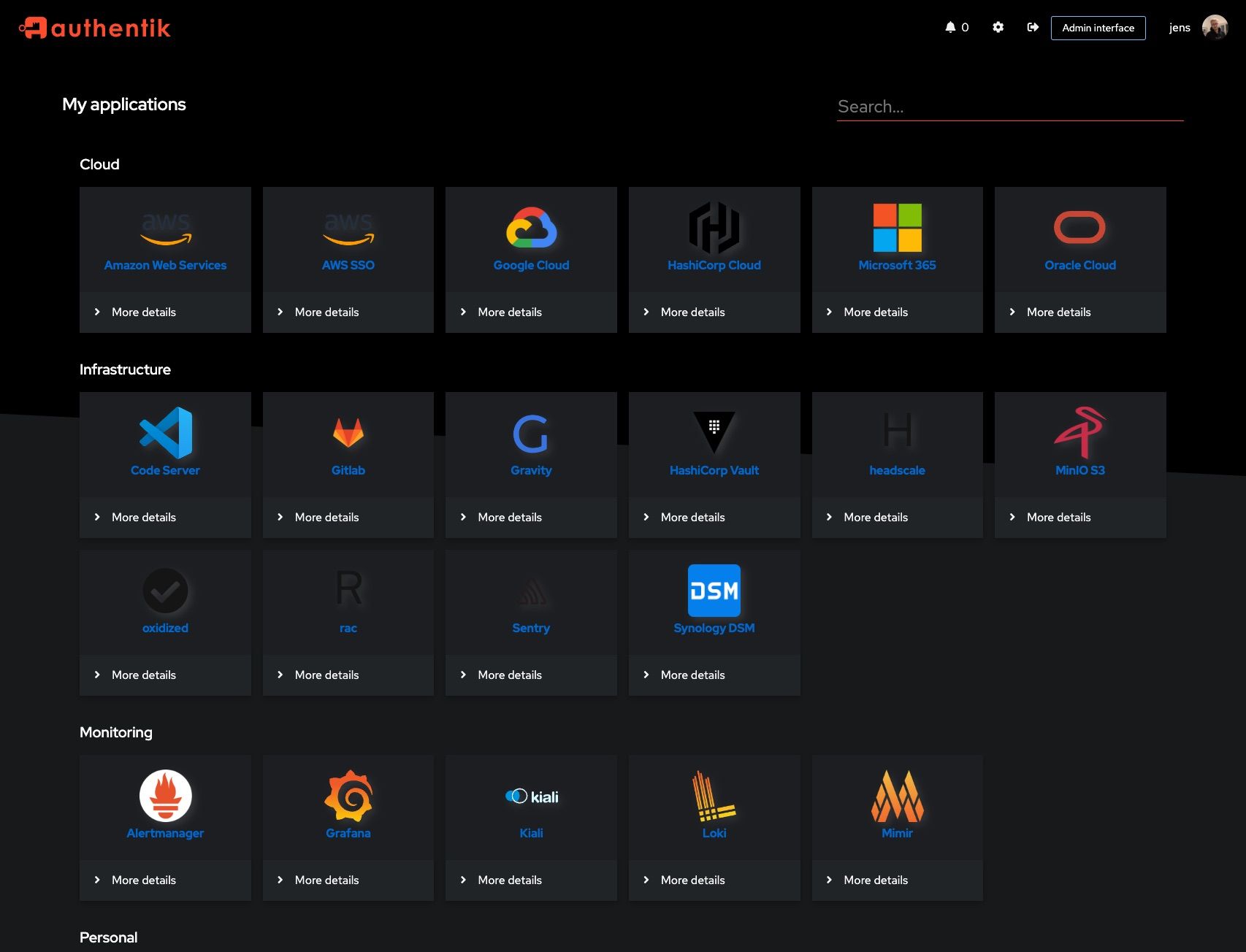 |
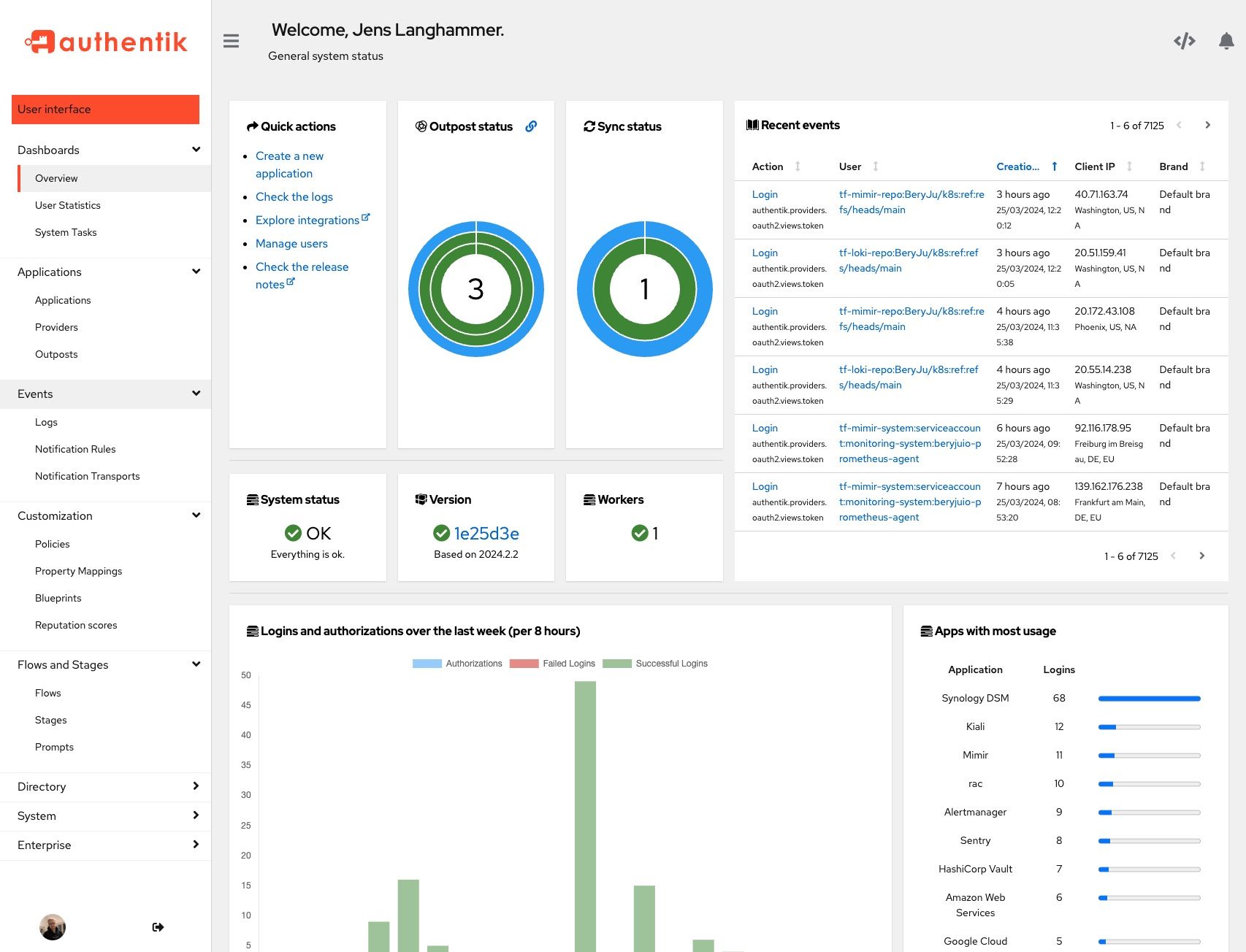 |
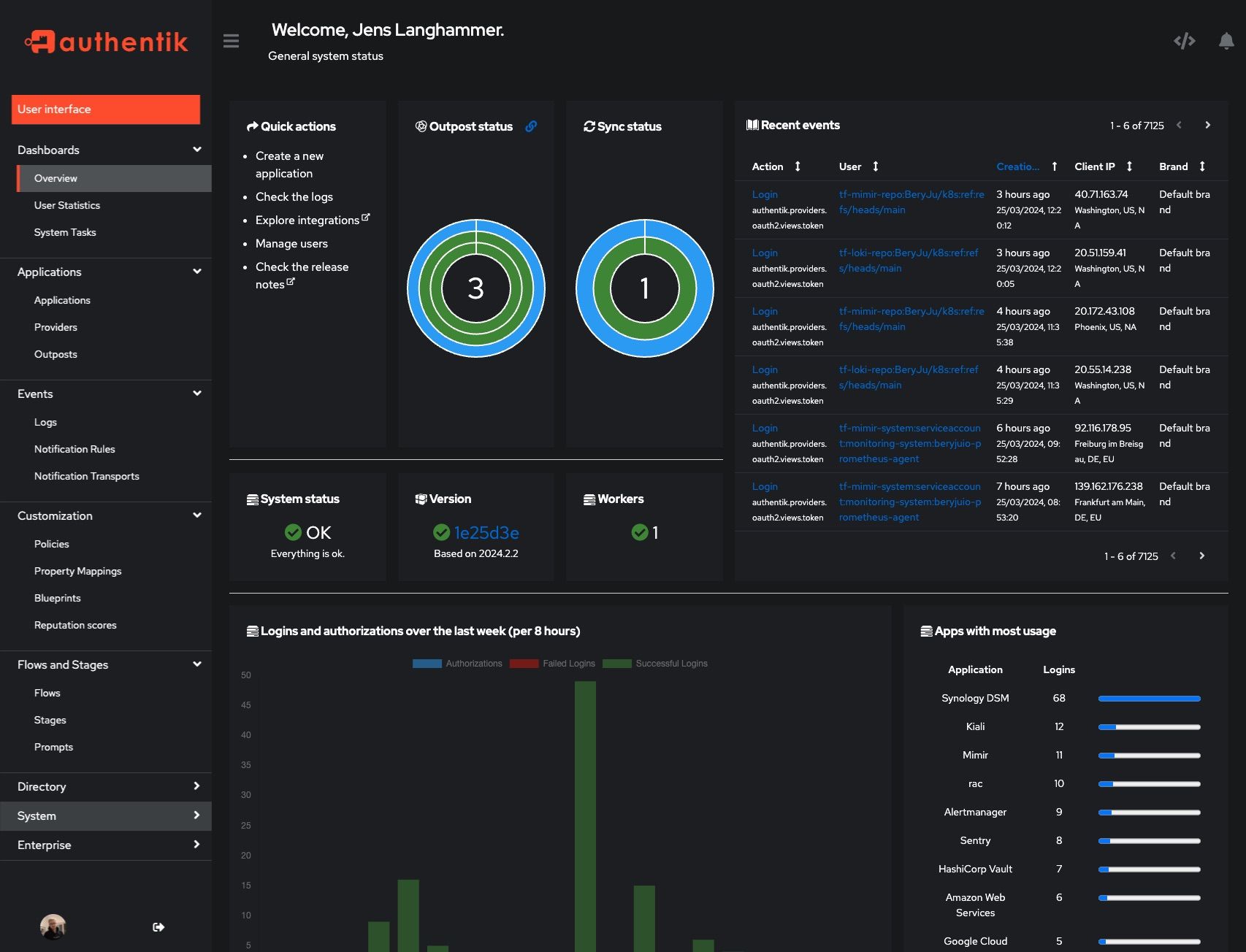 |
Development and contributions
See the Developer Documentation for information about setting up local build environments, testing your contributions, and our contribution process.
Security
Please see SECURITY.md.
Adoption
Using authentik? We'd love to hear your story and feature your logo. Email us at hello@goauthentik.io or open a GitHub Issue/PR!
License
Languages
Python
54.8%
TypeScript
34.7%
Go
4.3%
CSS
2.2%
Rust
1.9%
Other
2%









